Last week, I had the pleasure of participating in a webinar on automated shopping bots with Sandy Carielli, Security and Risk Analyst at Forrester Research. The webinar highlighted two things for me: automated shopping bots are a complex problem and they impact the entire business – not just security, or fraud or marketing.
Shopping Bots Pose a Complex Problem
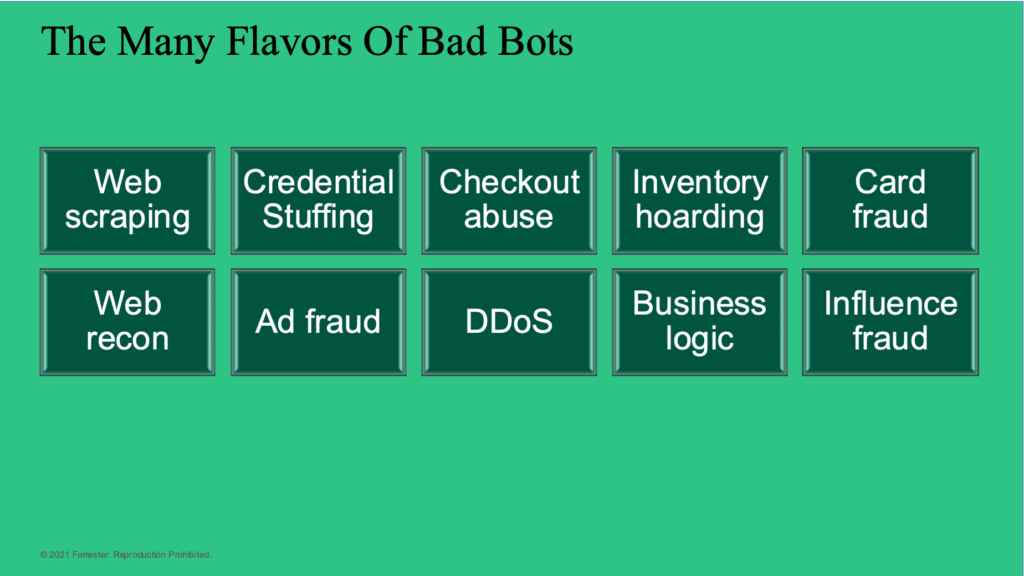
During the webinar, Sandy called out the different types of bad bots, from ATO to fake account creation to scraping, that her clients talk about. This is where the problem complexity comes to light. Advanced automated shopping bots and Bot-as-a-Service (BaaS) combine multiple bad bots from the list to execute their end goal.
Take for example a retailer that wants to sell 1,000 high-value/high-demand widgets. In order to ensure each of these widgets goes to a human rather than a bot, this retailer created a workflow where they raffle a single widget to every 100th checkout request. They have implemented traditional bot mitigation tactics including Google reCAPTCHA.
Prior to the sale, the threat actor will have already enlisted tools or BaaS platforms that have built-in reCAPTCHA bypass and they have reverse-engineered the embedded JavaScript or mobile SDK used to prevent the automated attack. Using BaaS forums the threat actor will know exactly when the sale will happen. During the attack, the threat actor will execute variations of the following attacks.
- Fake Account Creation – To maximize their chances in the raffle, BaaS will create hundreds, perhaps many thousands of fake accounts using automation. This puts pressure on the security, fraud and infrastructure teams as they deal with the influx of these fake accounts.
- Content and Inventory Scraping – BaaS want every advantage they can to get ahead of other bots and humans. One key aspect of that is to start shopping at the exact time the items go on sale. For that purpose, they start scraping the retailer to find out if that item is on sale. If the retailer has a dedicated sales event page, they keep scraping that page for updates, which is easier to manage. But if there is no dedicated sale event page, the bots scrape the entire site and look for updates to identify the start of the sale event. Once the widget goes on sale, the BaaS platforms need to keep track of the inventory so they will unleash the inventory checking bots that continually hit the APIs to determine if the inventory is available for sale. These automated actions put pressure on the infrastructure team which has to deal with a burst of bot traffic across the entire application tier.
- Shopping Cart and Checkout Abuse – Both of these elements are forms of API business logic abuse whereby widgets are loaded into shopping carts and when required, they “sign in” using the fake accounts created previously. Instead of using a scripted form fill, the threat actor will use the respective shopping cart and checkout APIs.
- Credential Stuffing – The result of the uptick in fake account logins for shopping cart and checkout abuse will appear to be a credential stuffing attack that will use email harvesting and CAPTCHA bypass to evade the techniques deployed to slow automated bots down. As with the fake account creation impact, the credential stuffing activity impacts the security, fraud and infrastructure teams as they deal with the influx of these fake accounts.
This example highlights the level of sophistication that malicious automated bot operators will go to in order to achieve their goals. No longer are each of these steps done manually – now using Bots-as-a-Service, the operators can easily turn their targets to any organization, not just retail.
Cross-Functional Impact of Shopping Bots
The second point Sandy made in the webinar was the impact that automated shopping bots have on the different personas, as shown in the image, within a retail business.

The key point made is that in some cases the groups are not collaborating, which happens in organizations both large and small, and as a result, the different groups may be unaware of the impact of bots outside their narrow window of visibility.
- The security team under the CISO organization could be focused on the Fake Account Creation and Credential Stuffing attacks, but it may not be aware that those large spikes in logins or account creation are related to the sales event.
- Scraping activity may be looked on as an infrastructure issue, addressed by increasing the capacity appropriately. The dots may not be connected back to the sale event, and the broader set of teams.
- The fraud team typically deals with payment fraud that results from Shopping Cart and Checkout abuse. Their anti-fraud systems will alert on the large volume of transactions coming in that are not real users. The impact is twofold – the high volume of fraudulent transactions tracked back to the fake accounts (illegitimate users).
- The team that is indirectly impacted by all this bot activity is the Marketing team, as various marketing KPIs are skewed by bots. For example – there are a lot more visitors for the sale than the marketing team anticipates and it may look like their ad campaign for the sale was highly successful. The spike in fake account creation may impact monthly active user KPIs, which in turn (negatively) impacts the checkout conversion rate.
- Public Relations and Branding Teams – The impact of an automated shopping bot on the PR team and the brand is typically the result of unhappy (real) users who made every effort to participate in the sale the instant it started, only to find out they missed out on the purchase because of a bot. Their frustration is vented on social media, resulting in brand and Net Promoter Score
- Ecommerce – When all is said and done, the true impact is on the loyal customers cannot be understated – according to Accenture, 57% of consumers spend more on brands to which they are loyal. That loyalty can generate between 12 and 18 percent incremental revenue growth per year than non-members. Research also shows that acquiring a new customer can cost 5 times more than the cost of retaining an existing one.
One could argue that if the teams were more collaborative, perhaps using the same tools, they may be able to exert mount a more effective defense against automated bots to help ensure their customers were able to succeed in making the purchase. Cequence API Spartan is helping retail customers minimize the business impact of automated shopping bots with a patented, ML-based platform that detects, tracks and ultimately blocks sophisticated bot behavior regardless of the evasive tactic employed. Don’t take our word for it – check out what our customers are saying in their Gartner Peer Insight reviews.




