The recent takedown of the RSOCKS botnet by the DOJ represents a small, but significant step in reigning in the use of high quality residential proxies for malicious purposes. Commonly referred to as a Bulletproof Proxy, these commercially available services market their database of compromised devices to cybercriminals as a pre-built infrastructure to execute large-scale attacks while masking their identity and location. Attackers will subscribe to the Bulletproof Proxy service then route their traffic through the network of devices to mask identity and location. Oftentimes, the same pool of compromised residential IPs will be used across many proxy services, as the proxy operators compete to commandeer infrastructure from one another. These services are billed as being used for web testing and other legitimate purposes, but the bulk of the use is to mask the identity and location of those who want to commit malicious acts. In the case of RSOCKs, the proxies are IoT and Android devices, oftentimes belonging to residential ISPs. Residential proxies are considered the gold standard for attackers, as they make the attack appear to be from a legitimate user making it difficult for defenders to block the attack without fear of (legitimate) user backlash.
Bulletproof Proxies in Action
A real-world example is an attacker who wants to score the newest Nike shoe will use RSOCKS to execute a large-scale shopping bot that emanates from multiple locations through many of these devices. This makes the traffic appear as if it is coming from legitimate buyers. Configuration options allow the attacker to distribute the traffic across the world, or focus it on a particular region – all in an effort to hide in plain sight. The attacker has the advantage of scale and speed in their favor, which typically results in them making the sneaker buy, and then reselling it for a significant markup. The scale of these automated attacks has been shown to result in reduced revenue due to their wide ranging business impacts that include:
- IT Infrastructure: Excessive load on the retailer web infrastructure resulting in site crashes and increased costs.
- Brand: Frustrated buyers vent on social media, resulting in lower net promoter scores.
- Employee frustration: Increased workload for teams who are tasked with fighting bots, not performing their daily tasks.
- Sales and Marketing: Errant business planning and marketing decisions based on falsely inflated web activity reporting.
Proxy services are used for any type of attack where the attacker wants to mask location and identity. Beyond shopping bots, there are other malicious use cases that include credential stuffing, account takeover, scraping, enumeration attacks and denial of service (DDoS). These services cater extremely well to those using bots to carry out their attacks, as the bad guys are trying to blend in a large flood of traffic amongst a pool of humans, instead of just a single attacking request.
Does the RSOCKS Takedown Matter?
RSOCKS was first observed in our customer base in 2019, with a pool of less than 200,000 proxies but they grew rapidly to where they recently had an advertised pool of 8M+ IPs. The growth was likely generated by exploiting unpatched vulnerabilities in the millions of (IoT and Android) devices connected to the web. For comparison, the larger proxy providers like SmartProxy and BrightData (formerly known as Luminati) claim access to a 40M+ IP address pool. Shutting down RSocks is not an insignificant development, but the reality is that their services will quickly be replaced by other providers including InstantProxies, SOAX, NetNut, and dozens of others, all of whom are commercial suppliers of these types of services. To truly reduce the number of attacks from Bulletproof Proxies, the community must harden the security of IoT devices, and work with ISPs to identify and patch vulnerabilities quickly as they arise.
Steps Users Can Take
The best thing users can do is to ensure their devices are not using default security settings, especially the factory default passwords shipped with routers. On top of that, set strong passwords, use two-factor auth, enable auto-update and disable sharing where applicable, especially for frivolous smart devices that in reality do not need wide network access permissions. If users notice home IP address being flagged as suspicious by their favorite websites and access being denied, then they should double-check the settings mentioned above to ensure they are not part of a Bulletproof Proxy network.
Turning Bulletproof Proxy Popularity for Defense
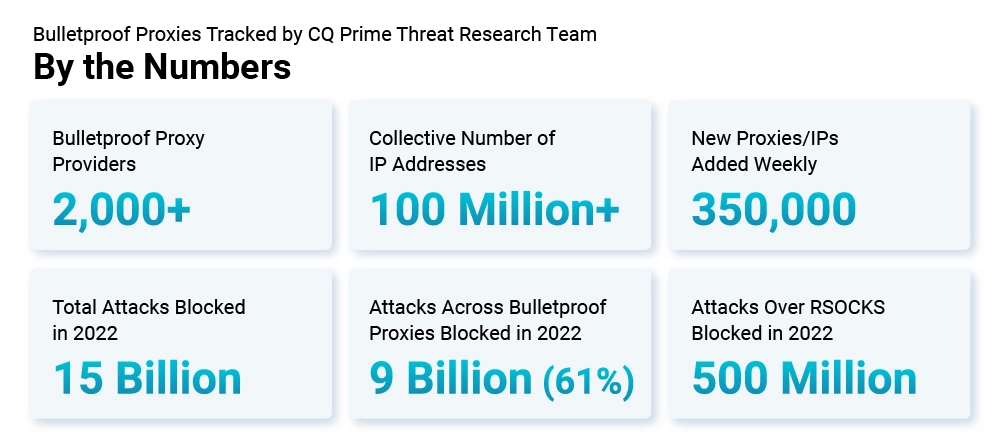
The Cequence CQ Prime Threat Research Team continually tracks more than 100 million malicious IP addresses distributed across more than 2000 organizations worldwide. These known malicious IP addresses are part of the Cequence API threat database with hundreds of millions of records that track attacker behavior, tools and stolen credentials. The API threat data is translated into hundreds of default policies that deliver industry leading out-of-the-box efficacy rates.
To see how Cequence API Spartan can use Bulletproof Proxies as defense tactic, sign up for a personalized demo today.
Sign up for the latest Cequence Security news
By clicking Subscribe, I agree to the use of my personal data in accordance with Cequence Security Privacy Policy. Cequence Security will not sell, trade, lease, or rent your personal data to third parties.



