Up until just a few years ago, web applications were the dominant platform for all things digital and APIs were tools used to address development corner cases. Driven by mobile device ubiquity, the adoption of the cloud, and the move towards agile, more iterative microservices-based development methodologies, APIs are now the connective tissue for everything we do digitally. The apps we use on our devices for work and pleasure, our favorite shopping, money management, travel web site, and even the cars we drive all use APIs heavily.
Built for machine to machine communications and inclusive of the desired function and payload, developers have come to love APIs for their ability to connect application elements and cloud services together quickly to create engaging user experiences. Attackers, who are developers at heart, love them for the same reasons, but with malicious end goals in mind. To dig into the details behind the explosive use of APIs, the security challenges they represent and how best to address those challenges, Cequence Security recently teamed with ESG to conduct a survey of 366 IT and cybersecurity professionals.
Containers and Cloud Drive API Growth
The survey found that over the next two years, organizations using APIs solely for their web and app development will nearly triple and 41% will use APIs for most of their development, nearly double that of today. Factors driving API usage include the move towards iterative, modular application development methodologies where APIs connect different components to each other. As a proof point, 71% of respondents stated that in two years, at least half of their apps would be microservices based, growing significantly from the current 39%.
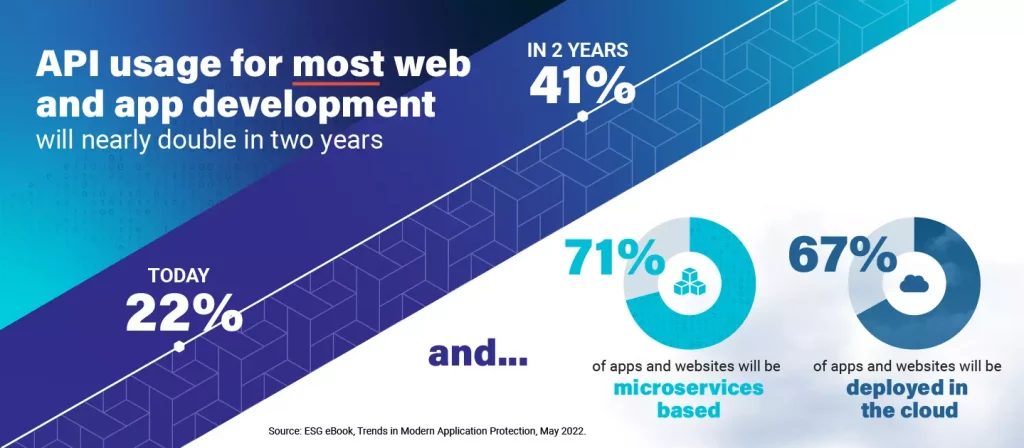
Validating the trend towards deploying the applications where it makes the most sense, cloud vs. datacenter vs. hybrid, 35% of organizations stated that 30% or more of their apps and websites were deployed in the cloud currently, growing to 67% of organizations in two years. In summary, the usage of cloud-native, microservices-based architectures will outpace the growth of cloud-resident applications, meaning many organizations will support hybrid application environments.
API Security Threats on the Rise
Highlighting the challenges that security teams face, the survey asked respondents to rank how frequently they saw thirteen different attack types in the last year and no single attack was seen more frequently than 34%. Each of the thirteen attack types can be executed against an API more easily than a web application, a fact that further solidifies the reasons why attackers love APIs. The attacks listed are often used collectively with one attack as a precursor to a second or third attack. As an example, an attack on misconfigured APIs (#7 on the list) may have been an exploit against misconfigured authentication or BOLA attack, ranked #1 on the OWASP API Security Top 10 list. The results of the BOLA attack could then be used in credential stuffing, account takeovers and fake account creation – all listed in the OWASP Automated Attack list.

The relatively tight grouping of the attacks found confirms the top API protection challenge organizations face: 41% of the respondents see keeping pace with the changing API threat landscape as their biggest challenge. Whereas the top challenge here is protection focused, the remaining challenges are more process focused and are indicative of how APIs have been developed and deployed. In the past, APIs were less widely used and developers had freer reign for where and when to deploy. In many cases, APIs were used internally, which meant less focus on security. Today, APIs are the heart of most organizations external facing digital footprint, but many of the past policies and procedures remain in place. This premise is supported by the need to apply more rigor to some of the other top challenges listed such as sensitive data handling (39%), keeping an accurate API inventory (37%) and the adoption of API specification frameworks (35%), which improves coding quality, consistency and security. Each of these challenges, if left unchecked, expose organizations to data loss, compliance violations and overall business disruption.
Gaps Remain Across the API Security Lifecycle
The current trajectory for API adoption and all that surrounds it is not that different than past technology adoptions, with some organizations much further along in the API lifecycle than others. Generally speaking, all organizations will begin their journey in one of the five phases shown below.
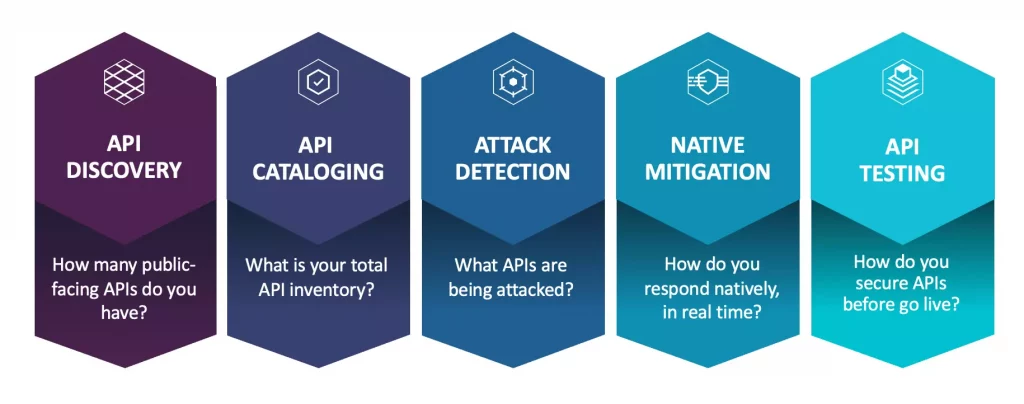
In some organizations, the journey begins in development as part of a DevOps effort, with an API testing tool. In other organizations it’s the security team who is tasked with responding to increased attacks on APIs. The varied starting points may help to shed light on the wide range of tools respondents were using to protect their APIs. The list included firewalls, WAFs, and IPSs as well as API security products. The range of tools highlights the nascent state of API security – with the survey confirming that no one offering provides effective coverage for the visibility, analysis, threat detection, mitigation and testing requirements that an ideal solution might deliver. Respondents indicated that their existing tools were woefully lacking in effectiveness, with less than 45% stating that their tools were completely effective – a failing grade in most anyone’s view. While the question was not specifically asked, one could argue that the wide range of tools, mostly all standalone and addressing only a piece of the puzzle may be one of the reasons for a lack of effectiveness.

An Opportunity for Consolidation
Organizations reported using a variety of tools to discover and secure their APIs highlighting that no one tool addresses all of the requirements, which may be the root cause of some of the challenges discussed previously. Further, for all the tools used for discovering and securing APIs, less than half of respondents rated them completely effective. The tools disparity introduces the opportunity for a unified or consolidated approach to API security. The survey points to a consolidated web and API (WAAP) framework as one approach but with an emphasis on API security. An alternative approach is to focus on the five phases of an API security lifecycle, and look for a unified solution to address the discovery, tracking, risk assessment, threat detection and prevention requirements. To gain additional insight into the API security challenges your peers are facing, and how they are looking to address them, download the ESG Trends in Modern Application Protection eBook today.
Cequence Security is helping customers transform their API security with an extensible, end-to-end API protection solution that prevents API threats while tracking and analyzing known and unknown APIs to surface vulnerabilities that help developers eliminate coding errors. Learn how Cequence is different.
Source: ESG eBook, Trends in Modern Application Protection, May 2022.