The Cequence Unified API Protection cumulative release (v5.2 to v5.4) adds new capabilities to enhance the export, categorization, and the prioritization of security events. In addition, there is enhanced rationalization of API endpoint discovery when multiple endpoints are found. These added capabilities further ensure the discovery and compliance of all your APIs, along with attack detection, prevention, and testing – as APIs are constantly added into your infrastructure.
Following are the key new features in this release of the Cequence Unified API Protection (UAP) solution:
Increased Visibility of Bot Detection and Mitigation into SIEM, SOAR Tools
Customers can now use Spartan to export bot detection events and bot mitigation events to a SIEM, SOAR or any other third-party tool that supports http-based integration. This type of integration will allow events to be exported to systems such as Splunk and Datadog.
This enables security analysts or fraud teams to ensure faster response and remediation of attacks on APIs by analyzing bot detection events and bot mitigation events by leveraging analytics features in SIEM or SOAR tools.
To accomplish the export of events, users create a data export configuration using the HTTP connector, specify the authentication credentials for the system receiving the data, and the types of events they want exported.
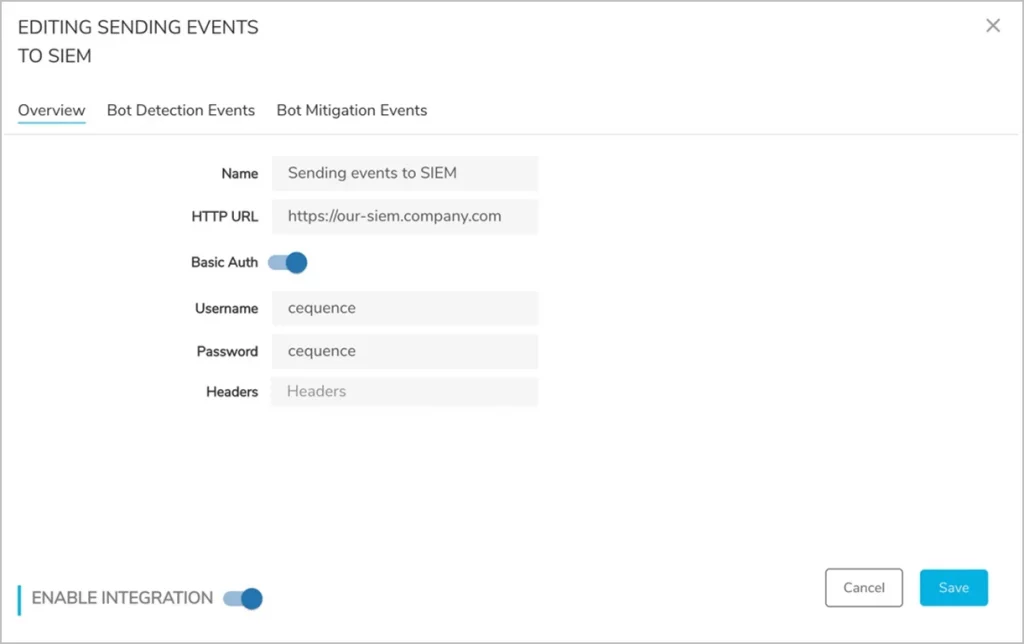
Creating a Data Export with the HTTP Connector
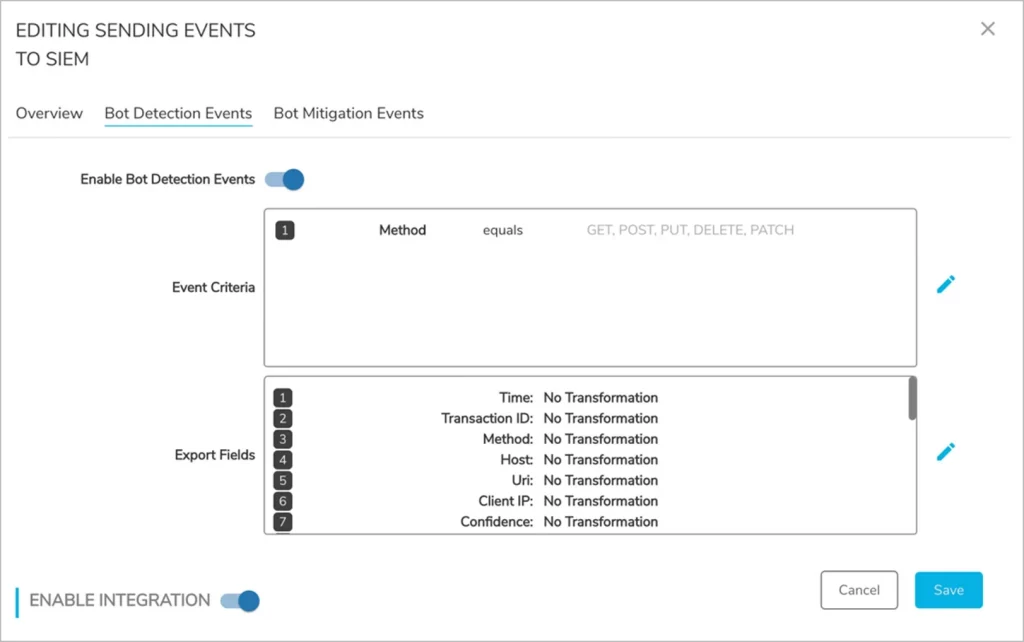
Defining Events to Export
Enhanced Mitigation of API Attacks by Eliminating Remediation Priority Conflicts
Spartan now has improved management of policies that determine the order of API attack mitigation. Spartan provides the ability to prioritize policies that help natively mitigate API security events. Every policy has a priority which determines the order in which policies will be applied by the Cequence Defender component; a low value means a policy has a higher priority than other policies and, therefore, will take precedence. With this new feature, Defender will now prevent a user from creating and saving a policy if there is already an existing policy with the same priority thus resulting in even higher efficacy in API attack mitigation.
New Summary Dashboard Streamlines Risk Assessments
Administrators can now quickly summarize the information API Sentinel has collected with a new summary dashboard to provide reports to executive teams. This dashboard helps quickly determine the number of APIs within a single domain or across multiple domains, as well as general characteristics of the API endpoints.
API characteristics include:
- Discovered (do not match any OpenAPI Definition)
- Published (included in an OpenAPI definition)
- Shadow (match an OpenAPI definition, but are not published in it)
The dashboard helps to identify what has recently changed in the environment so that an analyst can quickly determine what is new over preset times of 24 hours, 3 days, or 1 week. The summary dashboard can answer questions such as how many new API endpoints have been discovered in the last 24 hours or how many new risks have been uncovered over the last 1 week. The counts present in the dashboard are actionable allowing customers to click and link back into API inventory with a meaningful filtered view of the API endpoint.
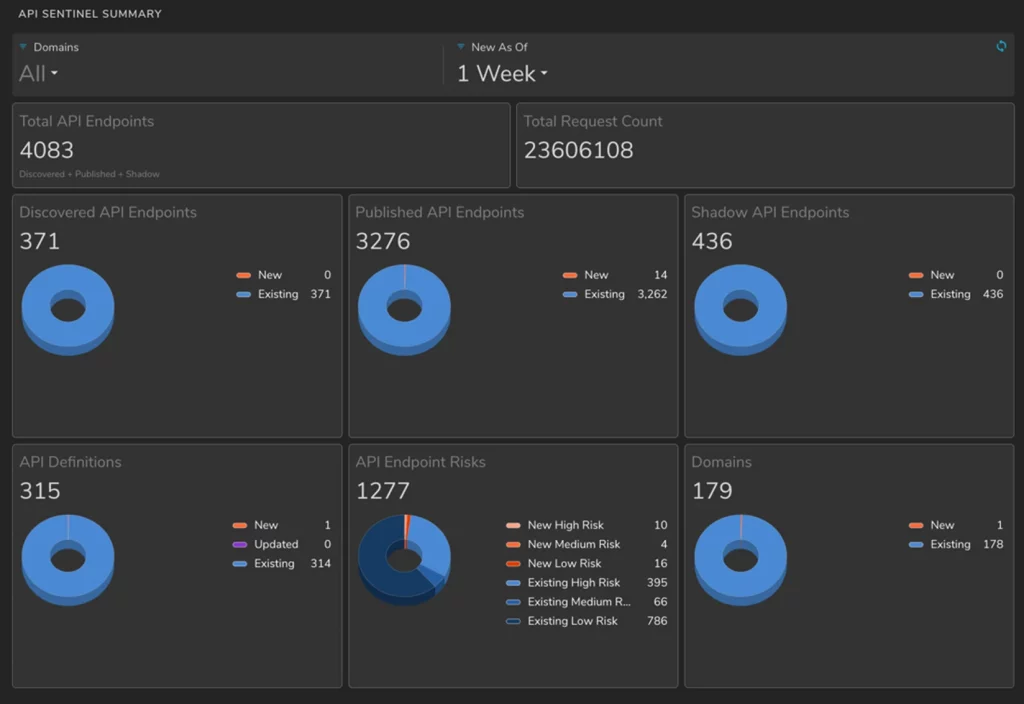
New API Sentinel Summary Dashboard
Watch the video to learn more about these new features and schedule a live demo
Better Understand Risk Based on OWASP API Risk Categories
This new feature allows users to use API Sentinel to flag API endpoints with OWASP API Top 10 risks using out-of-the-box risk categories.
API security has its own unique challenges compared to web applications. OWASP, the body that created the top ten for web application security, created a separate list for the top 10 API vulnerabilities. These are a community driven well known set of vulnerability categories relevant to APIs.
API Sentinel’s original default risk assessment and scoring is based on Access Control, Schema Non-Conformance, and Sensitive Data Exposure. These will now be grouped as V1 System Risk Categories and can continue to be utilized. But a new set of V2 System Risk Categories have been added that align with the more commonly understood OWASP API top 10.
The V1 System Risk Category rules have been redistributed and enhanced with additional functionality into the V2 System Risk Category rules. The new V2 rules can be enabled in place of the V1 rules to allow users to better understand risk detected by API Sentinel based on a more commonly used standard.
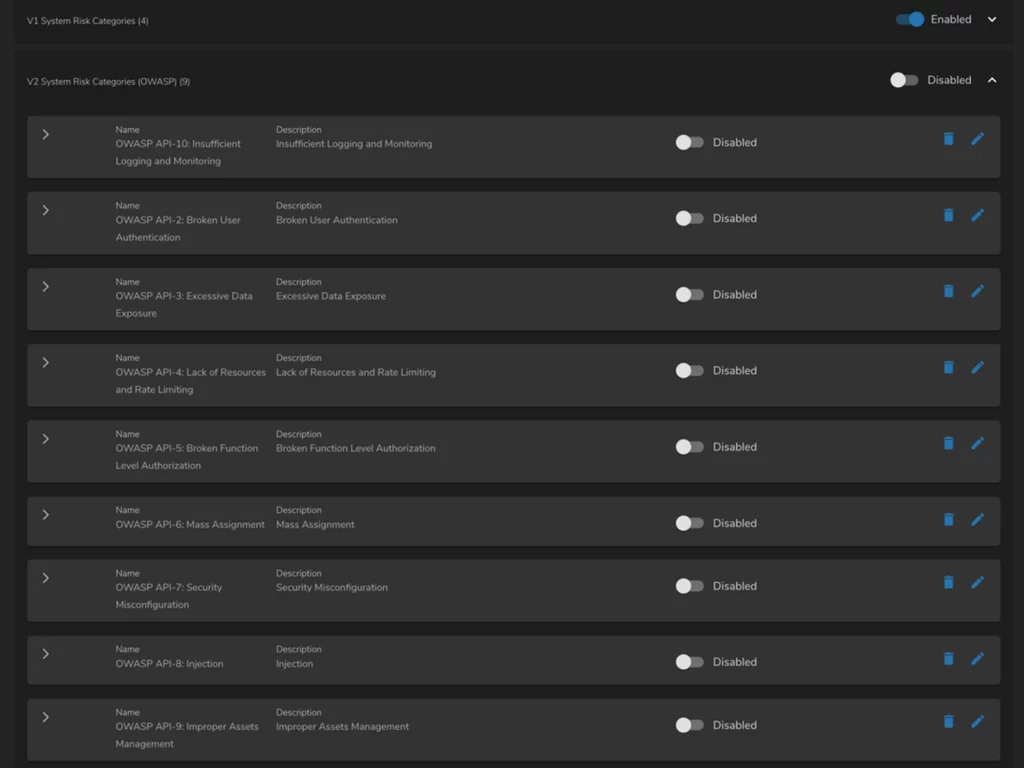
OWASP API Risk Categories
Data Export of Events for Additional Offline Analysis of Risk
A risk event is anything that triggers a rule as part of a Risk Category. The API inventory generalizes its analysis and provides metadata in place of the actual data. There are times where the actual data needs to be examined further. Data Export for API Sentinel introduces the ability to send specific informational details to third party systems for storage and further analysis. Custom configuration allows users to have granular control over what data they want to send to these third-party systems.
This feature helps application security analysts or risk teams analyze API risk information in offline analysis using a SIEM or SOAR system.
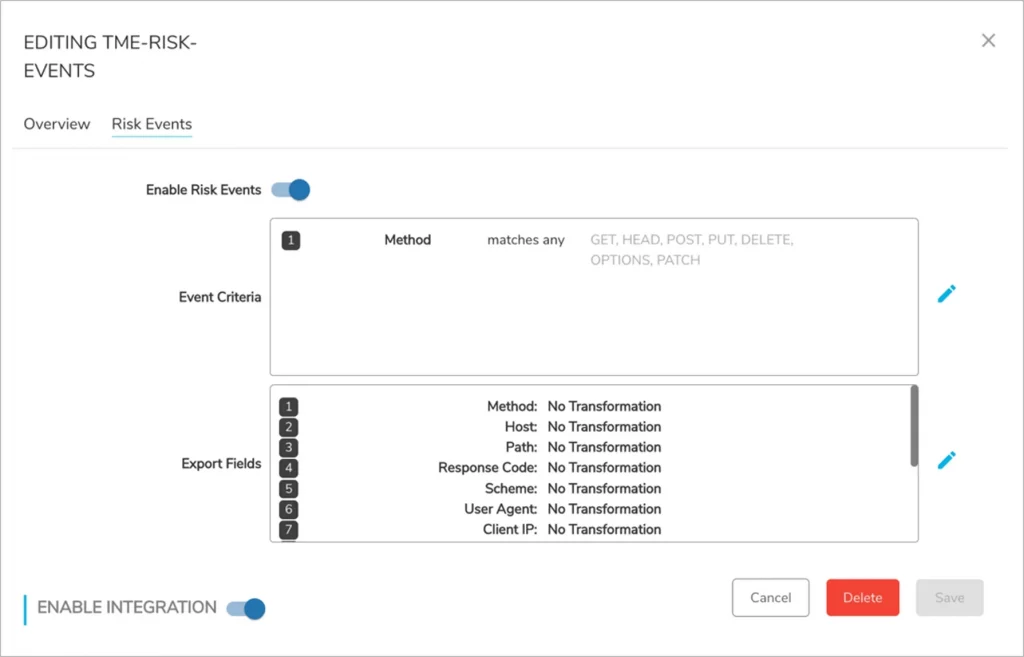
Data Export Configuration for Risk Events
Quickly Uncover Passwords Communicated in an Insecure Manner
API Sentinel users can now automatically discover API endpoints that use query parameters, body parameters, or request headers with the name “password,” indicating that password values are being communicated in an insecure manner from users to the API server.
This rule can also be generalized to create other such rules that look for field names with such text that might be concerning for a given application or use-case.
Risk categories have traditionally evaluated the VALUE in a KEY=VALUE pair in a header, body and/or query parameter, to access risk. With this new feature, risk categories can be configured to evaluate the component field names, the KEYS instead of their VALUES. The “password” field is one such example but can be generalized to look for any other pattern as well.
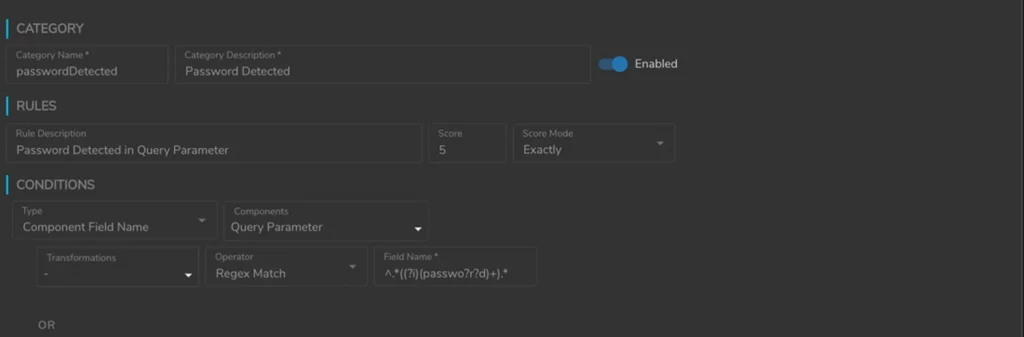
Predefined Password Field Risk Rule
Multiple Merge of Discovered Endpoints Helps Enhance Efficiency of Risk Assessment
Merging coalesces a discovered API endpoint into another discovered API endpoint which may better represent it. This is now automatically done by API Sentinel by analyzing the API endpoint paths and inferring the values that are parameterized.
In previous versions merging one endpoint with another was only possible for one API endpoint at a time. With this release, users are now prompted with additional, similar API endpoints which can also be merged into the same parent API endpoint. This enhances the user experience when attempting to merge multiple API endpoints and enhances efficiencies in risk assessment.
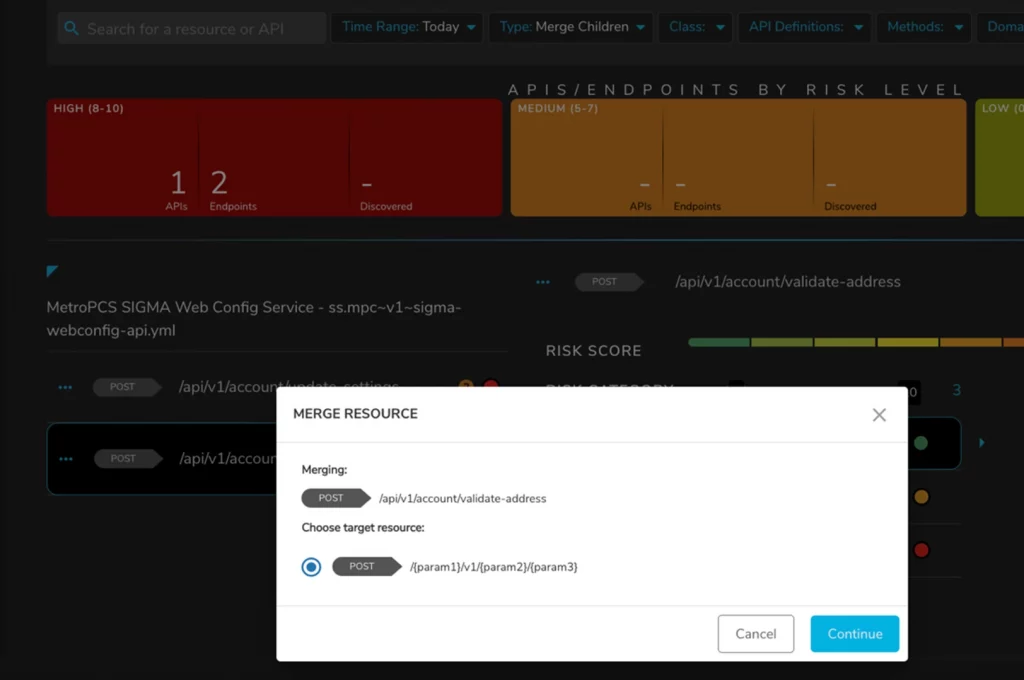
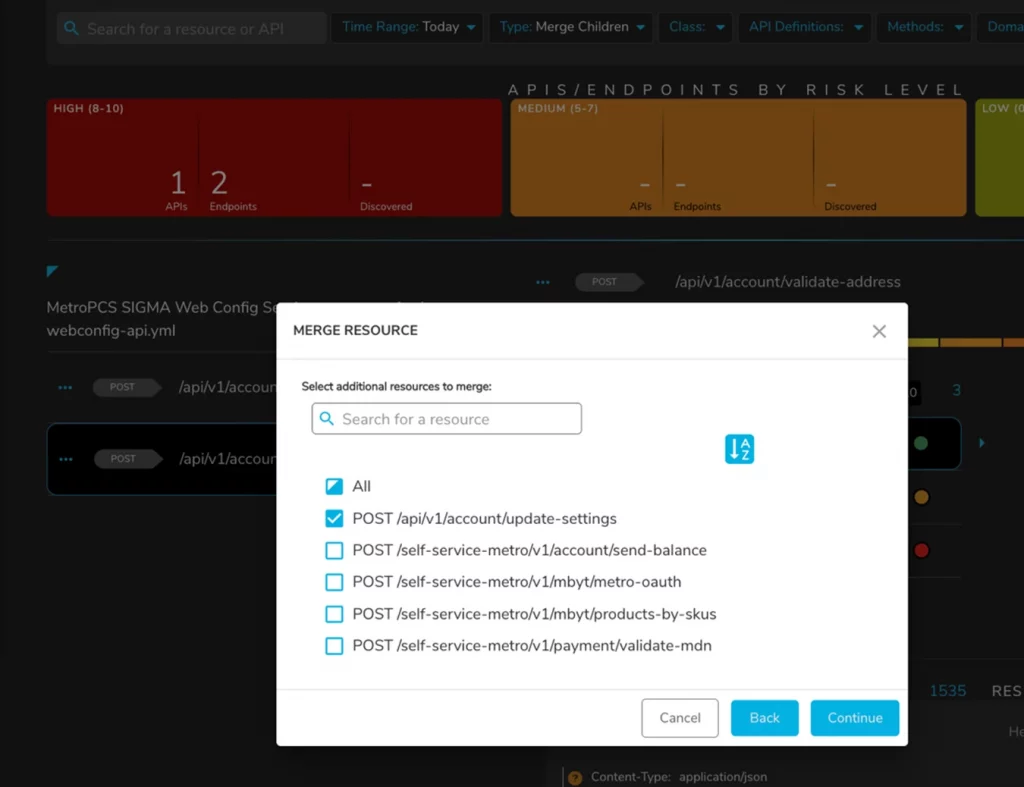
Multiple Merge of Discovered Endpoints
The Cequence Unified API Protection solution addresses the API security problem with a prevention first approach that natively detects and mitigates billions of attacks and vulnerabilities against APIs for our Fortune 500 customers every day.
Watch the video to learn more about these new features and schedule a live demo