The digital landscape is fraught with ever-evolving threats, making it crucial for organizations to stay informed about the latest trends in data breaches and cyber-attacks. The Verizon Data Breach Investigations Report (DBIR) serves as a valuable resource, providing deep insights into the current threat landscape. One crucial thing missing in the earlier versions of the report was the role of APIs in these incidents and breaches. We are pleased to announce that we were able to work with the Verizon DBIR team to plug this hole in the latest version of the 2023 Verizon Data Breach Investigations Report. We are also honored and humbled to be the ONLY API Security vendor in the industry to be mentioned in this prestigious report. Three key reasons for our inclusion were:
- Cequence owns the largest API threat database in the world.
- Data that Cequence provided was based on real threats as compared to theoretical survey-based data from other API Security vendors.
- 24% of Cequence customers are Fortune/Global 500; bringing representation from the largest organizations on the planet facing the most advanced attacks.
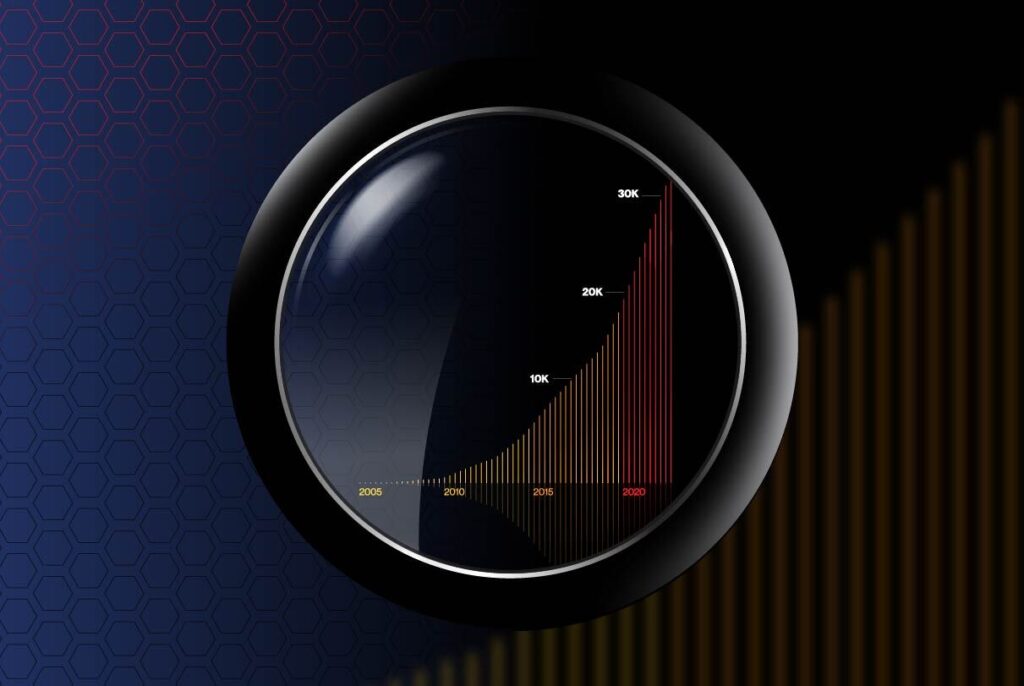
As software continues to eat the world and APIs continue to take the biggest bite, they will become more prominent on both the incident and the breach front for years to come. In this comprehensive blog post, we will dive into the findings of the latest Verizon DBIR, highlighting key facts and illuminating the critical role of Unified API Protection (UAP) in safeguarding web and other applications.
Where DBIR and API Security Intersect
Here are a few observations looking deeper into the DBIR to highlight API Security specific issues:
Social Engineering Attacks and the Rise of Business Email Compromise (BEC)
The Verizon DBIR underscores the effectiveness and profitability of social engineering attacks. Notably, Business Email Compromise (BEC) attacks, a type of pretexting attack, have witnessed a significant increase across their incident dataset, representing more than 50% of incidents within the Social Engineering pattern. These attacks leverage human vulnerabilities to manipulate individuals into divulging sensitive information or performing fraudulent actions. As most of these actions go over APIs, organizations can use UAP as a last resort to stop these fraudulent transfers even when BEC and other solutions fail to protect the user.
Web Applications as a Breach Point
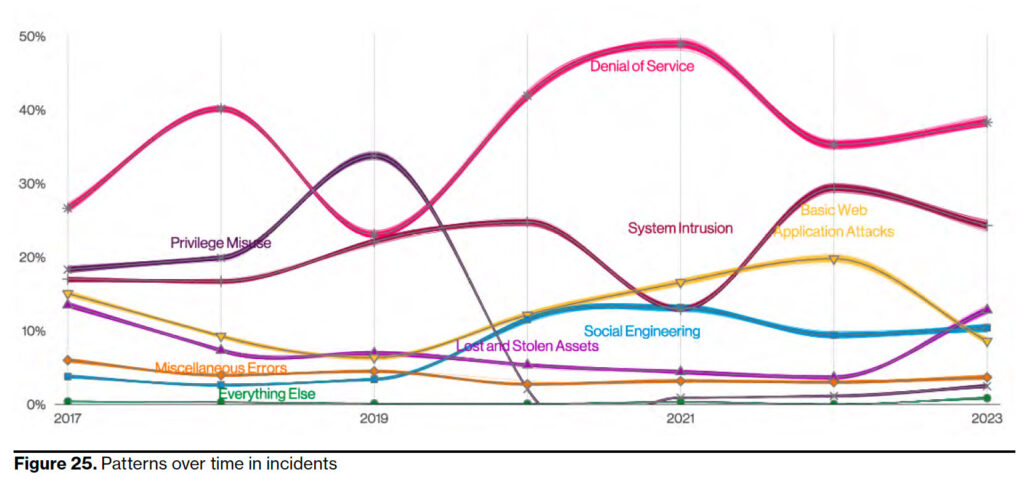
One of the most alarming findings of the Verizon DBIR is that a staggering 60% of all breaches occurred through web applications. According to Cequence Threat Research, as much as 80% of this web traffic comprises of API transactions. This statistic emphasizes the critical need for organizations to implement robust API protection measures. This observation is further substantiated by the 2H 2022 Cequence Threat Report, which delves deeper into the traffic analysis enabled by our advanced API Spartan detection module. Within the realm of web applications, our CQ Prime team encounters API security techniques such as fingerprint rotation, lack of human entropy, and session replay attempts on a regular basis.The report also emphasizes that DOS attacks are the primary action varieties affecting customer systems. This aligns with the research findings of the CQ prime threat research team. Public APIs belonging to our customers face highly voluminous attacks daily, with the goal of exhausting resources and causing outages. Fortunately, API Spartan platform incorporates a remarkably effective native mitigation module that successfully blocks these automated volumetric attempts. Not deploying multifaceted API protection can leave organizations vulnerable to exploitation by cybercriminals seeking to gain unauthorized access, steal sensitive data, or disrupt business operations.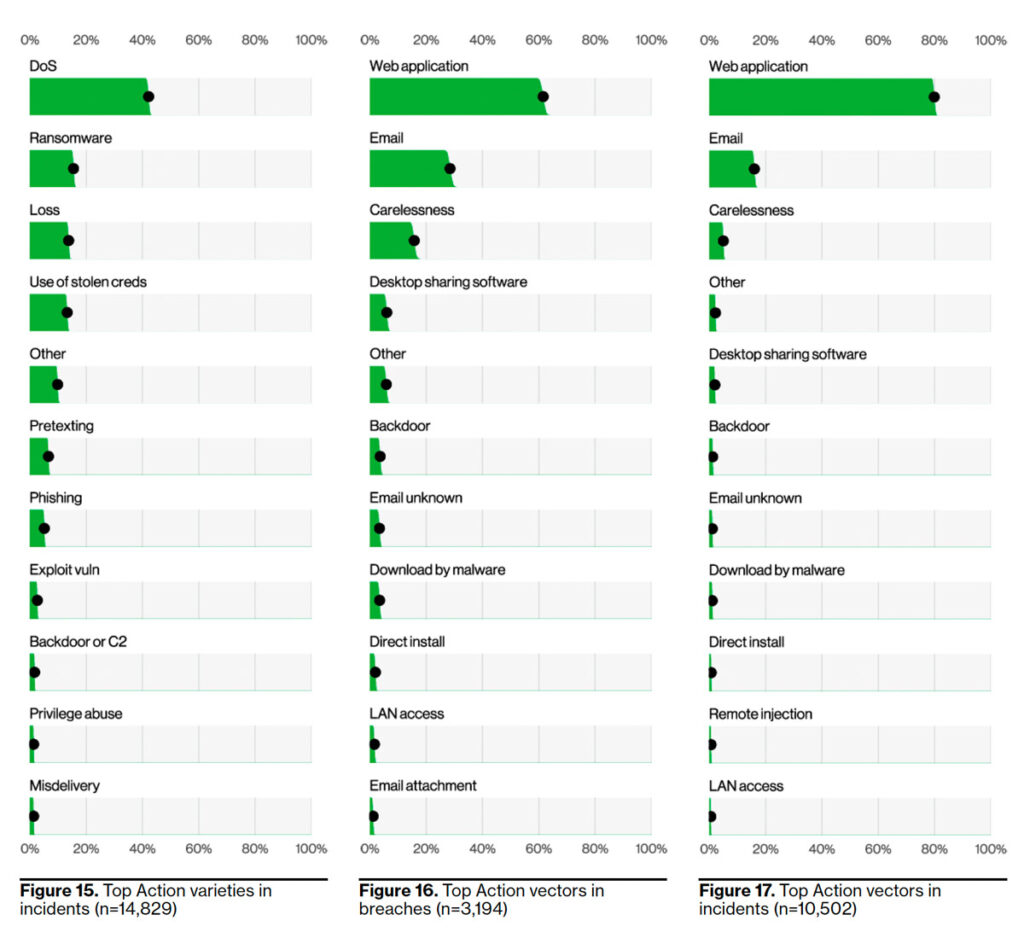
Understanding the API Attack Surface
The Verizon DBIR reveals that servers represented over 80% of all reported breaches. The utilization of APIs to access server data is growing exponentially. Within the realm of data breaches, the exfiltration of Personal Identifiable Information (PII) continues to reign as the most common occurrence. This assertion is strongly supported by the significant volume of threat events we consistently thwart on APIs that handle sensitive data, including operations such as authentication, authorization, credit checks, and payment flows. It is imperative for organizations to comprehensively understand their API attack surface, including the APIs exposed to the internet and their associated vulnerabilities. Cequence recognizes the criticality of API attack surface management and provides organizations with the tools necessary to gain visibility into their API ecosystem, identify potential risks, and proactively secure their APIs. 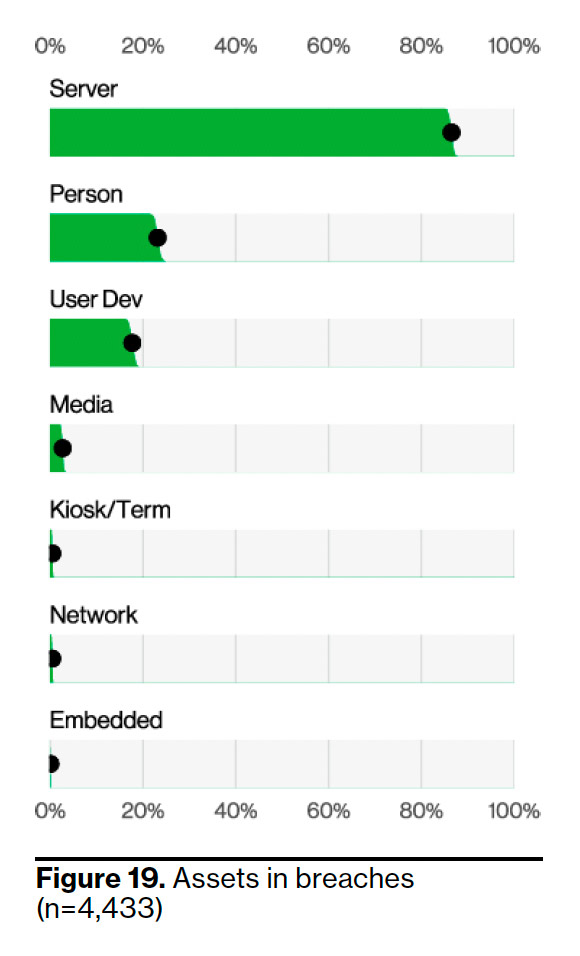
Addressing Developer and System Administrator Errors
Developers and system administrators play a vital role in the development and maintenance of applications. However, the Verizon DBIR points out that most errors leading to breaches are committed by developers (55%) and system administrators (40%). Cequence acknowledges the significance of addressing these human errors by implementing API security posture management and API security testing. These measures help organizations identify misconfigurations, coding errors, and vulnerabilities before they are released into production, thereby mitigating the risk of data breaches.
Combating Automated Attacks and Credential Theft
The Verizon DBIR highlights that basic web application attacks, including automated brute-force attacks, remain prevalent and successful. Additionally, a staggering 86% of web application breaches involved the use of stolen credentials. Cequence recognizes the importance of real-time threat detection and mitigation to counter these automated attacks and protect against account takeover (ATO) incidents. By leveraging advanced AI-driven technologies, Cequence offers organizations the ability to detect and block automated attacks, safeguarding against unauthorized access and potential data breaches.
Combining Effective BOT Strategy in API Security programs
According to the DBIR report and the CQ prime threat research database, ‘DOS’ and ‘Basic Web Application Attacks’ have consistently been among the most active threat patterns in recent years. This observation aligns with our findings in Q2 2022, where we also encountered similar patterns involving volumetric attempts on web applications and API security techniques. The DBIR report validates two significant themes highlighted in the Cequence reports:
- The importance of automated threat (BOT) mitigation in API security programs: The DBIR report supports our assertion that automated and native threat mitigation is of utmost importance in any API security program.
- The prominence of Web application and API Security TTPs (Tactics, Techniques, and Procedures) in attacker strategies: The DBIR report further substantiates our findings that attackers heavily rely on Web application and API Security TTPs when targeting APIs.
Linking MITRE ATT&CK Framework, Machine Learning and API Protection
No blog these days would be complete without mentioning AI (and specially generative AI) The top techniques identified in the MITRE ATT&CK framework, as highlighted in the DBIR report, align well with the machine learning (ML) rulesets that should be part of an effective API protection strategy. Cequence UAP platform ships with hundreds of ML models used to effectively block various malicious attempts, including Credential Stuffing, Password Cracking, Password Guessing, Password Spraying, Account Guessing, Application Access Token abuse, and Vulnerability scanning. Cequence UAP’s ML-based detection capabilities ensure that these events are swiftly detected and mitigated in real-time. By leveraging machine learning algorithms, our system not only identifies and responds to current threats but also stays vigilant against future attempts by constantly adapting and evolving its detection mechanisms.
Conclusion
The Verizon DBIR provides critical insights into the constantly evolving threat landscape, highlighting the need for organizations to prioritize robust web application security and API protection strategies. Cequence’s participation in the report underscores its commitment to addressing modern application attacks faced by Fortune and Global 500 companies. By recognizing the growing significance of APIs as an attack vector and offering comprehensive API protection solutions, Cequence enables organizations to protect their applications, prevent data breaches, and maintain the trust of their customers. As the threat landscape continues to evolve, it is imperative for organizations to partner with industry-leading API protection vendors like Cequence to fortify their defenses and stay one step ahead of cybercriminals. Together, we can secure the digital realm and protect invaluable assets from the ever-present risk of data breaches.
Get Your Copy of The API Threat Research Report
To learn more, download the full report API Protection Report in addition to the Verizon DBIR.