This year is turning out to be the year that kicks every company’s digital transformation into high gear in order to support work-from-home and shelter-in-place restrictions. With such a quick shift to and expansion of API-based architectures, it’s important to note the security vulnerabilities and expanded attack surface that are now interesting targets for bad actors.
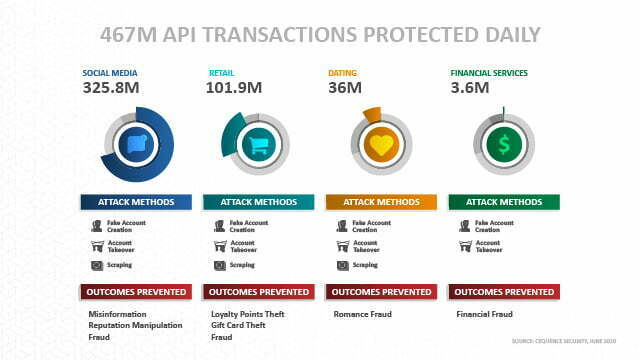
A recent analysis of our clients showed that across all industries – social media and entertainment, retail, dating, and financial services –attackers deploy various methods to abuse business logic or abuse APIs. Universally, they all experienced some form of an account takeover or fake account creation attack. And all but financial services were also hit with hard-to-stop content scraping attacks.
But, why are APIs such a common attack surface now?
Well, pretty much all the reasons developers love APIs are what makes hackers love them too. They are flexible, easy-to-use, and play nice with automation. So, armed with stolen credentials, bad actors can leverage a variety of tools to enumerate and discover your APIs and identify vulnerabilities that either give them access to accounts that can be taken over or to assume roles that give them more access to data or systems.
The good news is that with API protections in place, and the visibility needed to discover, assess, and mitigate API vulnerabilities also in place, you can make your web and mobile applicants an unattractive target for bad actors. Although some will be tenacious, the majority will move onto easier targets. And, these days, there are plenty more easy API targets out there.